Documentation Index
Fetch the complete documentation index at: https://auth0.generaltranslation.app/llms.txt
Use this file to discover all available pages before exploring further.
Demonstrating Proof-of-Possession (DPoP) を使用したトークンの送信者制約は、現在 Early Access の段階です。この機能へのアクセスをリクエストするには、Auth0 の担当者にお問い合わせください。
- クライアントの公開鍵 (
jwk)。 - メソッド (
htm) と URI (htu) を含む、アクセストークンリクエストを参照するペイロード。 - クライアントの秘密鍵を使用して作成された署名。
- リプレイ防止用の一意の ID (
jti)。 - 各 API リクエストごとの、アクセストークンの base64url エンコードされた SHA-256 ハッシュ (
ath)。 - オプション: の場合、クライアントアプリケーションが最近 DPoP Proof JWT を生成したことを示すための
nonceクレーム。
一般的なユースケース
- シングルページアプリケーション (SPA) とモバイルアプリケーション: パブリッククライアントである SPA やモバイルアプリケーションには、バックエンドサーバーのように を安全に保存できる、信頼された機密性の高い環境がありません。そのため、トークン窃取のリスクにさらされます。DPoP は、アクセストークンをクライアントアプリケーションの公開鍵にバインドし、DPoP Proof JWT を作成することで、このセキュリティ上の脆弱性に対処します。クライアントアプリケーションは、自身の秘密鍵で DPoP Proof JWT に署名し、それを認可リクエストで送信します。Auth0 認可サーバーは DPoP Proof JWT を検証し、有効であれば、発行するアクセストークンをクライアントの公開鍵にバインドします。
- サードパーティ API 連携: クライアントアプリケーションに統合された AI エージェントが、ユーザーに代わって DPoP Proof JWT を使用してサードパーティ API を呼び出す場合、 は、そのリクエストが不正な第三者ではなく AI エージェントから送信されていることを暗号的に検証できます。
サポートされているアプリケーションのグラントタイプ
| グラントタイプ | 説明 |
|---|---|
authorization_code | Authorization Code グラント |
client_credentials | Client Credentials グラント |
password | Resource Owner Password グラント |
refresh_token | Refresh Token グラント |
urn:ietf:params:oauth:grant-type:device_code | Device Authorization グラント |
http://auth0.com/oauth/grant-type/password-realm | 特定の realm を指定できる Resource Owner Password グラントに類似した拡張グラントを使用します |
http://auth0.com/oauth/grant-type/passwordless/otp | パスワードレス・グラントリクエスト |
http://auth0.com/oauth/grant-type/mfa-oob | MFA(多要素認証)OOB グラントリクエスト |
http://auth0.com/oauth/grant-type/mfa-otp | MFA(多要素認証)OTP グラントリクエスト |
http://auth0.com/oauth/grant-type/mfa-recovery-code | MFA(多要素認証)リカバリーコード・グラントリクエスト |
urn:ietf:params:oauth:grant-type:token-exchange | Token Exchange グラントリクエスト |
urn:okta:params:oauth:grant-type:webauthn | WebAuthn グラントリクエスト |
動作の仕組み
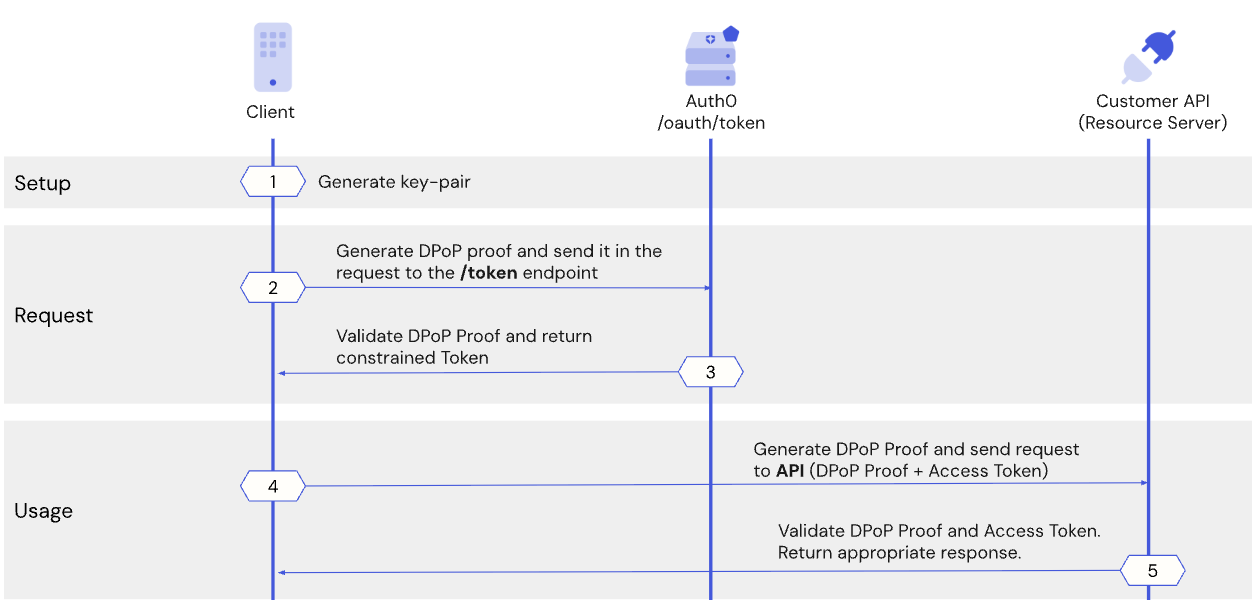
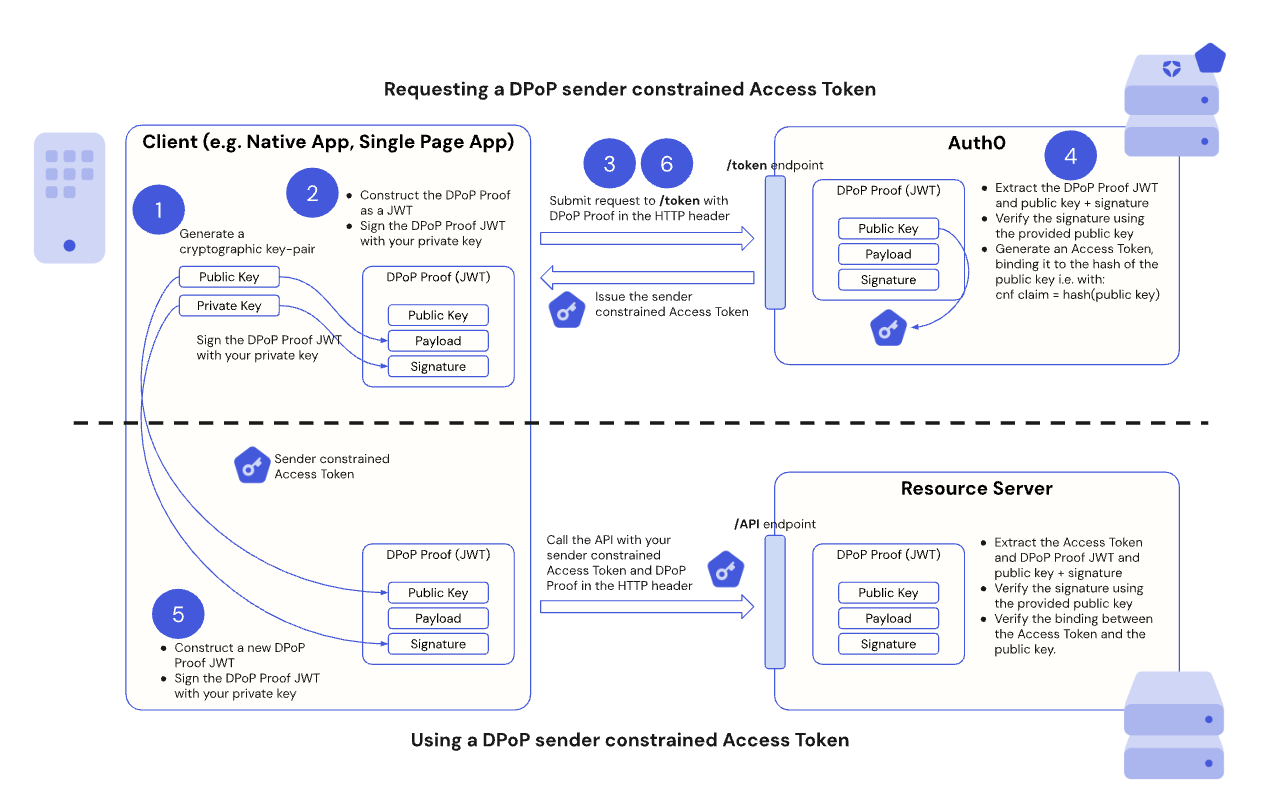
- Auth0 認可サーバーからアクセストークンを要求するとき、クライアントアプリケーションは一意の暗号鍵ペアを生成し、その公開鍵を用いて、自身が対応する秘密鍵を保持していることを証明します。
- クライアントアプリケーションは DPoP Proof JWT を生成し、それを Auth0 認可サーバー上の /token エンドポイントに送信します。
- Auth0 認可サーバーは DPoP Proof JWT を検証し、有効であればアクセストークンを発行し、それをクライアントの公開鍵にバインドします。
- Customer API を呼び出す前に、クライアントアプリケーションは新しい DPoP Proof JWT を生成し、トークンに関連付けられた秘密鍵を保持していることを証明します。クライアントアプリケーションは、DPoP Proof JWT と送信者制約付きアクセストークンをリソースサーバーに送信します。
- リソースサーバーは DPoP Proof JWT を検証し、トークンの正当な所有者、すなわち元のクライアントアプリケーションだけが保護されたリソースに正常にアクセスできるようにします。リフレッシュトークンからアクセストークンを要求する場合も、クライアントアプリケーションは新しい DPoP Proof JWT を生成し、リフレッシュトークンがクライアントの公開鍵にバインドされていることを保証します。
Auth0 で DPoP を使用してトークンを送信者制約する
- 前提条件
- ステップ 1: クライアントアプリケーションが DPoP キーペアを生成する
- ステップ 2: クライアントアプリケーションが DPoP Proof JWT を作成する
- ステップ 3: クライアントアプリケーションが DPoP バインドトークンをリクエストする
- ステップ 4: Auth0 認可サーバーが DPoP Proof JWT を検証する
- ステップ 5: クライアントアプリケーションが DPoP バインドトークンと DPoP Proof JWT を使用して API を呼び出す
- ステップ 6: DPoP を使用したトークンのリフレッシュを処理する
前提条件
- クライアント アプリケーションおよびリソース サーバーに対して sender constraining を構成 済みであること。
Step 1: Client application generates a DPoP key pair
ステップ 2: クライアントアプリケーションが DPoP Proof JWT を作成する
/token エンドポイントから DPoP バインドされたアクセストークンをリクエストする前に、クライアントアプリケーションは DPoP Proof JWT を作成する必要があります。DPoP Proof JWT は、クライアントの秘密鍵で署名された JSON Web Token (JWT) であり、「所持の証明 (proof of possession)」として機能します。
DPoP Proof JWT は、トークンリクエストにひも付くクレームを含む JWT ヘッダーとペイロードで構成されます。
JWT ヘッダークレーム
| DPoP Proof JWT クレーム | 説明 |
|---|---|
typ | dpop+jwt に設定します。 |
alg | RS256 や ES256 など、使用する非対称署名アルゴリズムです。 |
jwk | クライアントの公開鍵を JSON Web Key (JWK) 形式で表現したものです。 |
JWT ペイロードのクレーム
| DPoP Proof JWT クレーム | 説明 |
|---|---|
jti | リプレイ攻撃を防ぐための JWT の一意の識別子。 |
htm | DPoP Proof の対象となるリクエストの HTTP メソッド。たとえば、トークンリクエストの場合は POST、API 呼び出しの場合は GET。 |
htu | DPoP Proof JWT の対象となるリクエストの HTTP URI(フラグメントおよびクエリパラメーターを除く)。例: https://api.example.com/data?param=1#section1 は https://api.example.com/data になる。 |
iat | JWT の作成時刻(タイムスタンプ)。 |
ath | アクセストークンを使用する API 呼び出しの場合、そのアクセストークンの SHA-256 ハッシュを base64url エンコードした値。 |
nonce | nonce が必要なパブリッククライアントの場合、サーバーから提供される nonce 値。 |
ステップ 3: クライアントアプリケーションが DPoP でバインドされたトークンを要求する
/token エンドポイントにアクセストークンを要求する際には、リクエストの HTTP ヘッダーに DPoP Proof の JWT を含めます。
- 署名済みの DPoP Proof JWT を使用して DPoP HTTP ヘッダーを設定します。
- 署名済みの DPoP Proof JWT を含む DPoP HTTP ヘッダーを、アクセストークンリクエストで
/tokenエンドポイントに送信します。 - Auth0 認可サーバーからのレスポンスを処理します。
パブリッククライアント
/token リクエストを行い、DPoP HTTP ヘッダーに nonce の値を含めない場合、Auth0 は HTTP 400 コードと、次のようなエラーメッセージで応答します。
DPoP-Nonce ヘッダーを含めます。DPoP-Nonce ヘッダーの値を使用して DPoP proof を再生成し(Step 2 と同様)、その値を持つ nonce クレームを含めて /token エンドポイントへのリクエストを再送信する必要があります。
次のコードサンプルは、パブリッククライアントからの /token リクエストに nonce クレームを含めて送信し、その後に再試行するまでのエンドツーエンドのフローを示しています。
- Extracts the DPoP Proof JWT, its public key, and signature.
- Verifies the signature using the provided public key.
- Validates the
htm,htu,jti,andiatclaims. - If valid, it issues an access token. The Auth0 Authorization Server includes a confirmation claim,
cnf, in the access token. Thecnfclaim contains the thumbprint (hash) of the public key taken from the DPoP Proof JWT. By including it in the access token, the Auth0 Authorization Server binds the access token to that specific public key, or “sender-constrains” the access token. - Sets the
token_typein theAuthorizationheader toDPoPinstead ofBearerin the token response. Traditionally, when the access token is passed in theAuthorizationheader, it is set toBearer. However, because we’re passing an access token bound to a public key using DPoP, it is set toDPoPinstead. - The Auth0 Authorization Server then issues the DPoP sender-constrained access token to your client application.
ステップ 5: クライアントアプリケーションが DPoP バインド済みトークンと DPoP Proof JWT を使って API を呼び出す
- 次のクレームを含む新しい DPoP Proof JWT を生成します。
htmクレームは、GETやPOSTなどの、API リクエストのHTTPメソッドです。htuクレームは、API リクエストの URI です。athクレームは、ステップ 3 で受け取った DPoP バインド済みアクセストークンの base64url エンコードされた SHA-256 ハッシュです。
- クライアントの秘密鍵を使用して、新しい DPoP Proof JWT に暗号学的に署名します。
-
DPoP認証スキームを使用して、Authorizationヘッダーに DPoP バインド済みアクセストークンを含めます。
- 新しく生成された DPoP Proof JWT を
DPoPHTTP ヘッダーに含めます。
DPoP HTTP ヘッダーには、追加の ath クレームを含める必要があります。ath クレームは、発行されたアクセストークンの SHA256 ハッシュを base64url エンコードした値です。
リソースサーバーは次の処理を行います。
- API リクエストを受信し、アクセストークン、DPoP JWT プルーフ、公開鍵、および署名を抽出します。
jwkヘッダーに含まれる公開鍵を使用して、DPoP Proof JWT の署名を検証します。htm、htu、jti、iat、athクレームを検証します。- DPoP Proof JWT の
jwkヘッダーで示されている公開鍵が、アクセストークン内のcnf.jktクレームを介してアクセストークンにバインドされている公開鍵と一致することを確認します。
/userinfo エンドポイントを呼び出します。
ステップ 6: DPoP を使用してトークンを更新する
- Auth0 認可サーバーの
/tokenエンドポイントにリフレッシュトークンリクエストを送信します。 - リフレッシュトークンリクエスト用の DPoP Proof JWT を生成します([
htmをPOST、htuを の URI とする点が、ステップ 2と同様です)。 DPoPHTTP ヘッダーに DPoP Proof JWT を含めます。
- DPoP Proof JWT を(ステップ 4と同様に)検証し、新しい DPoP によってバインドされたアクセストークンを発行します。
Important considerations
- Private key security: The security of your DPoP implementation depends on the security of your client’s private key, so you must protect it from unauthorized access. Private keys should be generated and stored in a hardware-backed medium and marked as non-exportable.
- Replay protection (
jti** anddpop-nonce):** Thejticlaim in the DPoP Proof JWT helps prevent replay attacks for protected resources, such as the/userinfoendpoint. The Auth0 Authorization Server currently does not checkjtireuse on the/userinfoendpoint. The Auth0 Authorization Server issues aDPoP-NonceHTTP header in its response, which public clients must include as anonceclaim in subsequent DPoP Proof JWTs for enhanced replay protection. - Error handling: You are responsible for implementing logic to handle DPoP-specific errors from the Auth0 Authorization Server or resource server, such as
invalid_dpop_prooforuse_dpop_nonce. - Client types: Use DPoP for public clients, such as Single Page Applications (SPAs) or mobile apps that cannot securely store a client secret. For , such as backend services with client secrets, DPoP adds a layer of security, but they already have other sender-constraining mechanisms.
- Performance: Because generating and signing DPoP Proof JWTs for every API call adds a small overhead, ensure your client application’s cryptographic operations are efficient.
- Key rotation: Implement a strategy for rotating your DPoP key pairs for enhanced security. Make sure you use the same key pair for the same session.
- Persistence: For client applications that need to maintain a session and reuse DPoP-bound access tokens, such as long-lived SPAs, securely persist and retrieve the original generated key pair across application reloads. If a new key pair is generated or a different key pair is used, the DPoP-bound access token becomes invalid, as it is cryptographically tied to the public key of the original pair. You can persist the key pair, for example, in a browser’s
IndexedDBor a mobile app’s secure storage.